Combining Tracing, Metrics and Logs for High-Level Cybersecurity
These three elements work together to provide a complete and detailed view of infrastructure behavior and detect any suspicious or anomalous activity that may pose a security threat.
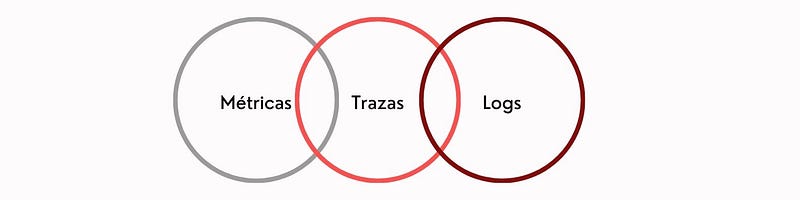
- Tracing: Tracing is like a “live video” that records events and activities in real time on the network. They act as a digital detective, tracking and capturing detailed data about the flow of information in the infrastructure. The traces generated by probes and network devices provide a complete view of network activity. Redborder uses these traces to quickly detect security incidents and respond nimbly to any threats.
- Metrics: Metrics provide key indicators of network performance and offer aggregatable information on health and resource utilization. They allow you to assess the overall health of the network and detect anomalies or potential problems before they become real threats. Redborder uses metrics to proactively monitor the network and keep it secure and efficient.
- Logs: Logs act as a “detailed diary” of events and activities on the network. They contain valuable information about the behavior of the infrastructure and are generated by network devices and security solutions. Redborder uses logs to understand the context of events and improve visibility into network activity. By correlating logs from various sources, such as operating systems and applications, Redborder can gain a more complete view of the threat landscape.
And how do we do it at Redborder? Well, here comes the magic! Redborder intelligently combines all these pieces of the puzzle with a SIEM module, allowing you to centralize and manage all logs, even those coming from third-party vendors. This ensures that no important detail goes unnoticed and improves incident detection and response.
But that’s not all, we also provide you with clear and detailed visualizations so you can easily understand what is happening in your network. With our platform, you can make informed and quick decisions to protect your cybersecurity services.
In short, the relationship between traces, metrics and logs in Redborder’s services provides centralized and advanced network observability. The combination of these three elements enables early threat detection, proactive response to security incidents and a deep understanding of network behavior. With Redborder, enterprises and service providers can keep their digital infrastructures protected and respond quickly to security challenges in an increasingly complex and changing environment.